This article is more than 1 year old
USA can afford golf for Trump. Can't afford .com for FBI infosec service
So guess what spoofers are doing with the fake site? Yup – getting dupes to log in
InfraGard.org is supposed to be one of the United States' defences against online criminals. But the FBI-led service is currently the subject of a typosquatting and email attack that could see organisations seeking protection instead send their personal data straight to parties unknown.
As its name implies, InfraGard is all about protecting American infrastructure. The organisation does so by linking the FBI with “businesses, academic institutions, state and local law enforcement agencies, and other participants dedicated to sharing information and intelligence to prevent hostile acts against the U.S.”
The organisation boasts 84 chapters, more than 54,000 members and says more than 400 of the Fortune 500 have someone who works with InfraGard. Members get to share information security information in a closed environment, providing each other and the FBI with useful intelligence.
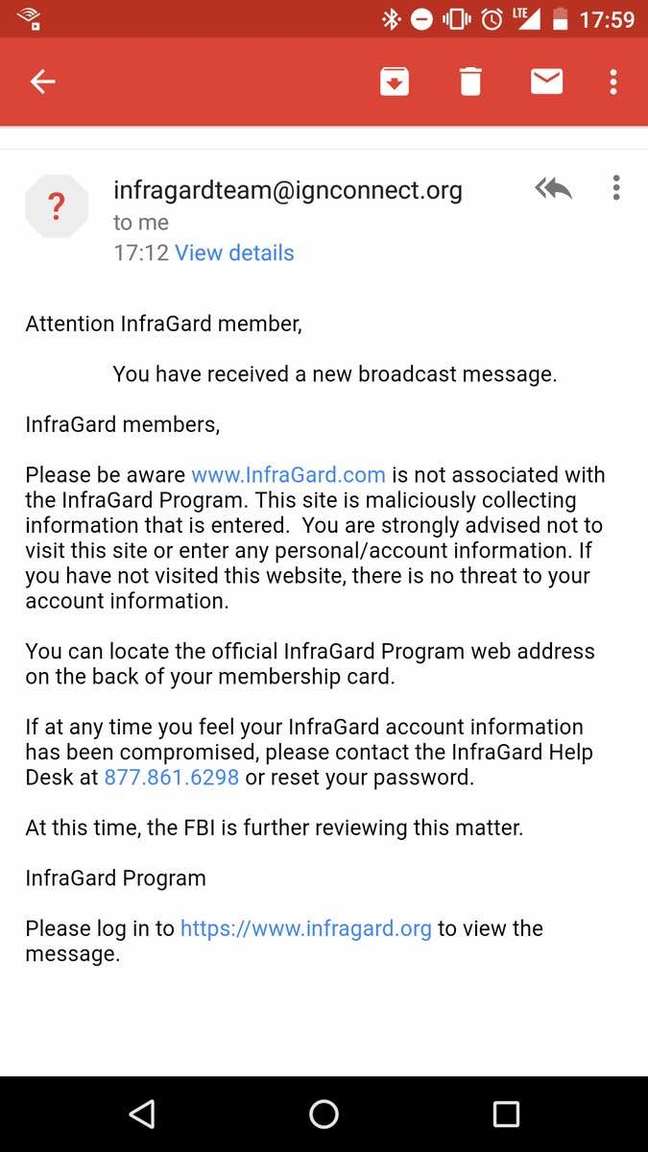
Phish sent to InfraGard members. Click here to embiggen
In other words, this is a serious organisation with an important mission.
But not serious or important enough to have acquired the infragard.com domain.
We know about this omission because over the last few days folks have been sharing emails luring them to the fake infragard.com, which offers a passable replica of the real InfraGard site and asks visitors to log in.
This website is impersonating the #FBI-run #InfraGard? - Change #Chrome to tell you - #cybersecurity #infosec https://t.co/LBHuuuaz2R
— Ivan Piacun CITPNZ (@IvanPiacun) March 26, 2017
The good news, according to security researched David Longenecker, is that the fake site appears not to be sharing data with any other. Even if it is not, it could be building a nice trove of logins. Infosec types should know better, but what's the bet some of the IDs and passwords the fake site harvests will work elsewhere?
Others believe the fake site is winning users' trust by actually logging them in to the real site, with bait-and-switch tactics.
Longenecker says the FBI is aware of the fake site. And so it should be: a Whois search shows it was first registered in 2002 and offers a contact at Lunacorp.com. Don't visit that domain, dear readers, it offers only dodgy weight loss data. It also appears that the site changed hands quite recently, making the timing of the email campaign a fascinating co-incidence.
The deeper question is why the FBI hasn't squashed the typosquatting site, even if it has long been dormant. Mechanisms exist to do reclaim domains. You'd think that the FBI, of all entities, would have sussed them out years ago.
For the rest of us, the attack is easy to defeat, as the fake site uses HTTP and the real thing uses HTTPS. The most recent versions of top browsers will therefore point out that the connection to the fake InfraGard.com is not secure. Once you notice that warning, feel free to flee, stylishly, in pursuit of the real thing. ®
