This article is more than 1 year old
Domain name resolution is a Tor attack vector, but don't worry
Nation-state attackers probably pwn you anyhow
This one needs the words “Don't Panic” in large friendly letters on the cover: privacy researchers have worked out that Tor's use of the domain name system (DNS) can be exploited to identify users.
However, they say, right now an attacker with resources to drop Tor sniffers at “Internet scale” can already de-anonymise users. Rather, they hope to have Tor and relay operators start hardening their use of DNS against future attacks.
So: read if you're interested in the interaction between Tor and the DNS, but not if you need the sensation of smelling salts after a faint.
The basis of Tor is that your ISP can see you're talking to a Tor node, but nothing else, because your content is encrypted; while a Tor Website is responding to your requests, but doesn't know your IP address.
What Benjamin Greschbach (KTH Royal Institute of Technology) and his collaborators have done is add the DNS to the attack vectors.
While the user's traffic is encrypted when it enters the network, what travels from the exit node to a resolver is a standard – unencrypted – DNS request.
Described at Freedom to Tinker here and written up in full in this Arxiv pre-print, the attack is dubbed DefecTor.
Google's DNS has a special place in the research, the paper states, because 40 per cent of DNS bandwidth from Tor exit nodes, and one-third of all Tor DNS requests, land on The Chocolate Factory's resolvers. That makes Google uniquely placed to help snoop on users, if it were so minded.
There's a second problem, and one The Register is sure has other researchers slapping their foreheads and saying “why didn't I think of that?”: DNS requests often traverse networks (autonomous systems, ASs) that the user's HTTP traffic never touches. The requests leak further than the Tor traffic that triggers it.
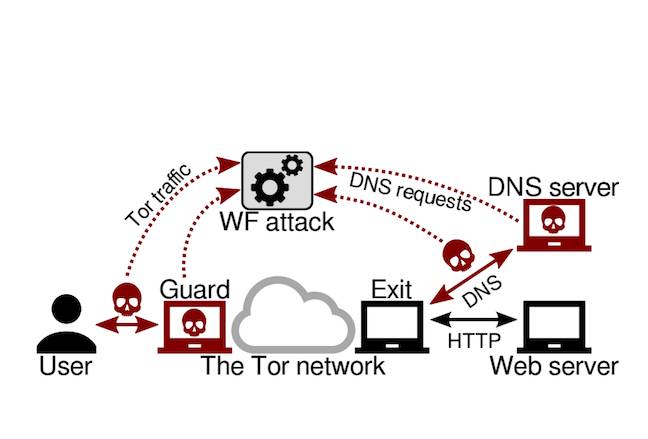
DefecTor components: a sniffer on the ingress TCP traffic, and another either on the DNS path or in a malicious DNS server
Like other attacks, DefecTor needs a network-level sniffer at ingress. While ingress traffic is encrypted, existing research demonstrates that packet length and direction provides a fingerprint that can identify the Website that originated the traffic.
Egress sniffing is also needed: the attacker might capture traffic on the path between an exit relay and a resolver; or may operate a malicious DNS resolver to capture exit traffic.
With the user's encrypted TCP traffic fingerprinted, DNS requests, and time-stamps, DefecTor can mount “perfectly precise” attacks.
“Mapping DNS traffic to websites is highly accurate even with simple techniques, and correlating the observed websites with a website fingerprinting attack greatly improves the precision when monitoring relatively unpopular websites,” the paper states.
Mitigations suggested in the paper include:
- Exit relay operators handling DNS resolution themselves, or using their ISP's resolver, rather than Google or OpenDNS;
- There's a “clipping bug” in Tor (notified to the operators) that expires DNS caches too soon, sending too many requests out to a resolver (and providing more sniffable material to an attacker);
- Site operators should create .onion services that don't raise DNS requests; and
- Tor needs hardening against Website fingerprinting.
The researchers have published code, data, and replication instructions here. ®l
