This article is more than 1 year old
On her microphone's secret service: How spies, anyone can grab crypto keys from the air
Boffins decode 'coil whine' while encryption code runs
Discerning secret crypto keys in computers and gadgets by spying on how they function isn't new, although the techniques used are often considered impractical.
A new paper demonstrates this surveillance can be pretty easy – well, easier than you might imagine – to pull off, even over the air from a few metres away.
We all know that tiny fluctuations in electrical current during encryption routines, or even the sounds made by the system, can be picked up wirelessly to ascertain keys used – just ask the NSA. However, it usually requires hooking up expensive analysis equipment and takes long periods of time to gather all the bits needed.
Now, in a paper published by the Association for Computing Machinery, researchers from Tel Aviv University have detailed how inexpensive kit can be used to harvest 4,096-bit encryption keys from distances of around 10 metres (33 feet).
These are the same boffins who hid a loop of wire and a USB radio dongle in a piece of pita bread last year and used it to steal keys over the air.
In their latest research, the team managed to pick up encryption keys using acoustics. As a computer's processor churns through the encryption calculations, the machine emits a high-frequency "coil whine" from the changing electrical current flowing through its components.
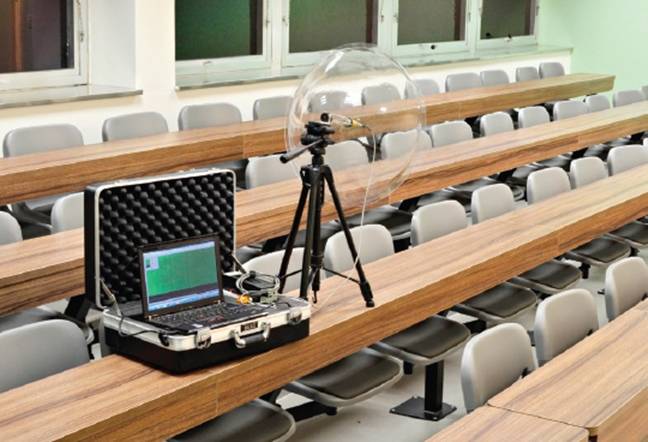
The boffins' mic setup ... Not exactly subtle, but effective
By using a parabolic mic, the team was able to pick up the coil whine from 10 meters (38 feet) away. Trouble is, that mic is a little obvious if you're trying to be sneaky, so they managed to get the same result from a mobile phone's microphone placed 30 centimetres (12 inches) away from the spied-on PC. In both cases it took an hour of listening to get the 4,096-bit RSA key.
On the one hand, this still isn't a very practical attack, and most people shouldn't fear it. You have to train a mic on a device for an hour while it runs cryptographic software over and over, and without background noise ruining the key capture. On the other hand, you may be paranoid enough to consider mitigating it.
To combat this security hole, you need tweak your software, the team suggested. It's possible to use acoustic dampening inside a PC against sound attacks, Faraday cages to block electromagnetic emissions, and insulation of the enclosures of laptops. But this isn't practical in the real world.
Instead, the team recommends encryption software writers build in "blinding" routines that insert dummy calculations into cryptographic operations. After discussions with the team, GNU Privacy Guard now does this.
So it's not all bad news, but the research does serve as a reminder that you don't just need to check your software for security, but scout around the hardware too for mysterious gadgets. ®
