This article is more than 1 year old
All smartwatches are insecure, reveals unsurprising research
100 per cent – yup, ALL – contain significant vulns
Update A study by Hewlett Packard (HP) has revealed that a hefty 100 per cent of smartwatches contain significant security vulnerabilities.
As part of HP's extended shuftie over the Internet of Things thing, the company has unveiled a new report (PDF) in which it confirms that wristjob wearing wallies are even wider open to cyberattacks than they are to being ridiculed in The Register.
The study said that it could not find a single smartwatch which didn't show shoddy security implementations, including naff authentication, and what can only be described as a cultural allergy to crypto.
HP's researchers also noted (as the WWWs often don't) that it is the express function of these products to attempt the complete remediation of any notion their users' might have of privacy.
"Smartwatches have only just started to become a part of our lives, but they deliver a new level of functionality that could potentially open the door to new threats to sensitive information and activities," said Jason Schmitt, general manager, HP's Security Fortify.
"As the adoption of smartwatches accelerates, the platform will become vastly more attractive to those who would abuse that access, making it critical that we take precautions when transmitting personal data or connecting smartwatches into corporate networks," added Schmitt.
Wear your vulnerabilities on our sleeve
HP's hackers had their way with 10 of the leading wristjob products, and concluded that the results "were disappointing, but not surprising."
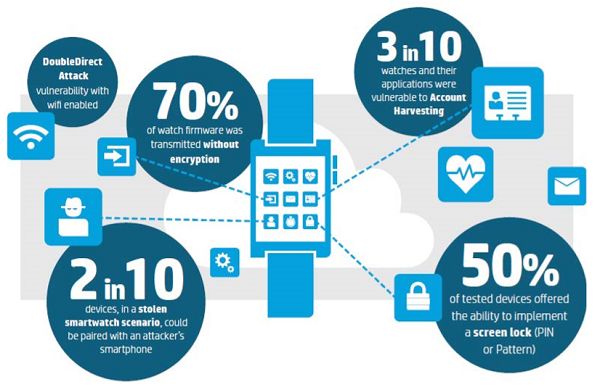
Their work managed to turn up the usual issues, from privacy through to account harvesting, as well as firmware updates happening in the clear, but turned up some interesting cock-ups too, including that running a DNS service on one of the watches allowed it to be used as part of a DNS amplification attack.
While the issues listed below are not present in all of the smartwatches, they provide a snapshot of some of the vulnerabilities disclosed in several models:
Insufficient Authentication/Authorisation: The researchers found that three of the smartwatches completely failed to offer two-factor authentication, while also requiring eight-character alphanumeric passwords. All three of these smartwatches were unable to lock out accounts after 3-5 failed login attempts.
Insecure Network Services: While all of the watches connected via Bluetooth to their parent device, only four offered the ability to connect to Wi-Fi for notifications when out of that device's reach.
One Wi-Fi watch had a functioning DNS server running, which allowed DNS Amplification attacks to be performed against other targets on the network.
That particular product was also vulnerable to the DoubleDirect attack, a Man-in-the-Middle attack utilising the ICMP Redirect attack to view a victim's network traffic.
Lack of Transport Encryption: While all products implemented transport encryption using SSL/TLS, the hackers found that 40 per cent of the cloud connections are either still vulnerable to the POODLE attack, allowing the use of weak cyphers, or using SSL v2.
Insecure Software/Firmware: 70 per cent of the wristjobs had issues when it came to the protection of firmware updates. These included transmitting updates without encryption, and without encrypting the update files.
HP concludes: "Our research shows that these wearables present a risk that goes beyond the device. The number of places that data are being sent during the standard use of a given application increases the number of access points."
"Whether using a health application, financial, or even gaming application, HP was able to intercept and detect the sensitive data being routed to multiple locations on the net."
In other words: uh-oh. ®
Update
HP have contacted us with the following statement: "In line with our responsible disclosure policies, we do not release the names of the companies, products or models tested. Our practice is to notify the affected companies and provide them with an opportunity to address the security issues uncovered by our testing. As part of the report however, we do provide recommendations for both consumers and enterprises looking to use or produce smartwatch devices in a more secure manner."
