This article is more than 1 year old
Researchers tell black hats: 'YOU'RE SOOO PREDICTABLE'
Want to register that domain? We're way ahead of you.
Security geeks have worked out a formula for determining which of a series of formerly blacklisted domains would be reused in malware attacks.
The method combines the domain name with the generic Top Level Domain, IP address alterations and the cost of a domain transfer.
Under the right conditions, the researchers sway, the domains net villains plan to use could be blocked or otherwise used to in the service of good instead of evil.
Palo Alto researchers Wei Xu, Yanxin Zhang and Kyle Sanders presented the paper We know it before you do: predicting malicious domains [pdf] at this week's Virus Bulletin conference.
Much effort has been put into building reputation-based malicious domain blacklists, however in order to evade detection and blocking by such systems, "many malicious domains are now only used for a very short period of time" they write.
"In other words, a malicious domain has already served most of its purpose by the time its content is detected and the domain is blocked.
"... we propose a system for predicting the domains that are most likely to be used (or are about to be used) as malicious domains. Our approach leverages the knowledge of the life cycle of malicious domains, as well as the observation of resource re-use across different attacks."
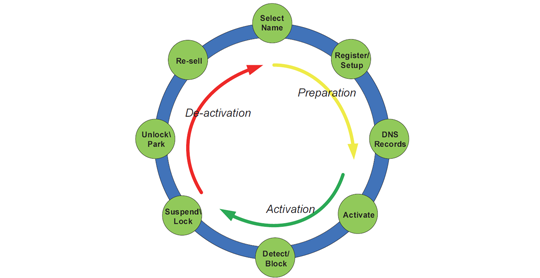
Life cycle of a malicious domain
The trio observed attackers reused valuable resources in setting up malicious domains and built in to their formula knowledge of the malicious domain life cycle. They designed systems to leverage Domain Generation Algorithms (DGAs) which could automatically predict future malicious domain names, and found temporal patterns in DNS queries of the malicious domains before their use.
Shared hosting IP addresses, DNS resolution infrastructure and shared domain registration information allowed domains to be identified that have not yet but would very likely be used in future attacks.
Malware flingers were increasingly taking advantage of resources geared to reuse given the economic benefits, which fell right into the hands of researchers.
"The reuse of resources across different attacks also presents opportunities for us to find connections between malicious domains," they said. "Using our knowledge of these connections, we can identify domains that are setting up to be used for malicious purposes."
They said the technique could predict and prevent malicious domains which could become stronger with future work.
The work did not consider benign domains that were hacked to host attacks, and focused crosshairs on bulletproof hosts. ®
