This article is more than 1 year old
TrueCrypt turmoil latest: Bruce Schneier reveals what he'll use instead
Plus other alternatives and theories behind disk-crypto util's demise
The TrueCrypt project abruptly imploded on Wednesday – leaving folks in the infosec world scratching heads and scrambling to recommend alternatives.
In the past hour, crypto-guru Bruce Schneier has told us he's switched back to Symantec's PGPDisk to encrypt his data.
"I have no idea what's going on with TrueCrypt," he added on his blog. "Speculations include a massive hack of the TrueCrypt developers, some Lavabit-like forced shutdown, and an internal power struggle within TrueCrypt. I suppose we'll have to wait and see what develops."
As The Register reported, visitors to the official truecrypt.org website were redirected to a SourceForge-hosted site, which warned the popular multi-platform disk-encryption software is insecure:
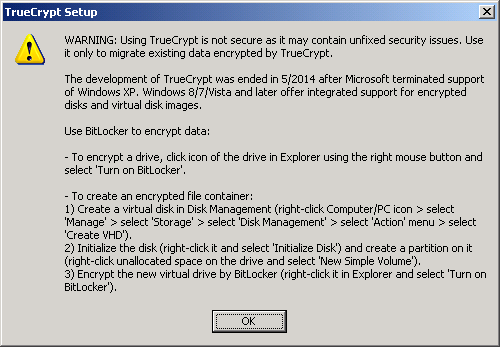
WARNING: Using TrueCrypt is not secure as it may contain unfixed security issuesThis page exists only to help migrate existing data encrypted by TrueCrypt.
The development of TrueCrypt was ended in 5/2014 after Microsoft terminated support of Windows XP. Windows 8/7/Vista and later offer integrated support for encrypted disks and virtual disk images. Such integrated support is also available on other platforms (click here for more information). You should migrate any data encrypted by TrueCrypt to encrypted disks or virtual disk images supported on your platform.
The above message is included in the developer-signed executables of a new version of TrueCrypt, released this week and available now from the SourceForge site; version 7.2 pops up an alert during installation urging the user to migrate files away from the easy-to-use tool:
This new build has been nobbled to prevent further encryption of data. It should not be relied upon to safeguard sensitive information. The previous version, 7.1a, was released in 2012.
At first, the truecrypt.org switcheroo appeared to be an act of web vandalism by miscreants who had compromised the super-secretive TrueCrypt development team.
But the inclusion of the above warning in the cryptographically-signed binaries strongly suggests that the message did really come from the anonymous developers of TrueCrypt – or whoever is in possession of its private key.
Matthew Green, a computer-science professor at Johns Hopkins University in Maryland, US, commented: "I think it's unlikely that an unknown hacker identified the Truecrypt developers, stole their signing key, and hacked their site."
Prof Green and Kenn White, a cloud security expert and engineer, are spearheading an effort to audit the source code of TrueCrypt 7.1a, which is available to download and build. Last month the software successfully cleared the first phase of an independent code-quality inspection, which “found no evidence of backdoors or intentional flaws”. A grassroots campaign raised $70,000 to pay for the professional audit, funds that the latest developments would suggest may have been wasted. An unrelated announcement on the audit project's progress was due to be made today.
"Our board is meeting this morning, and should have announcement mid-day on our plans. I think the community will be happy with the direction we're going," White told The Register.
